Boosting your iPhone's security, iOS 18.1 introduces a new feature to protect your data after periods of inactivity. This update incorporates a crucial safeguard for your device and its encrypted information.

The Inactivity Reboot Feature
Apple's iOS 18.1 introduces the Inactivity Reboot feature, automatically restarting your iPhone after three days of inactivity while locked. The Secure Enclave Processor (SEP) monitors your iPhone's unlock status. If locked for an extended period, the SEP triggers a reboot, effectively shutting down the iOS core (Springboard).

Why This Matters for Data Protection
This reboot enhances data protection by clearing encryption keys from memory. The iPhone enters a secure "at rest" state, making decryption extremely difficult. Even if powered on for a long time, this feature prevents outdated forensic tools used by hackers from accessing your sensitive data.

Law Enforcement Implications
While beneficial for privacy, this feature poses challenges for law enforcement's forensic analysis. However, research suggests the three-day window provides sufficient time for coordination to access devices.

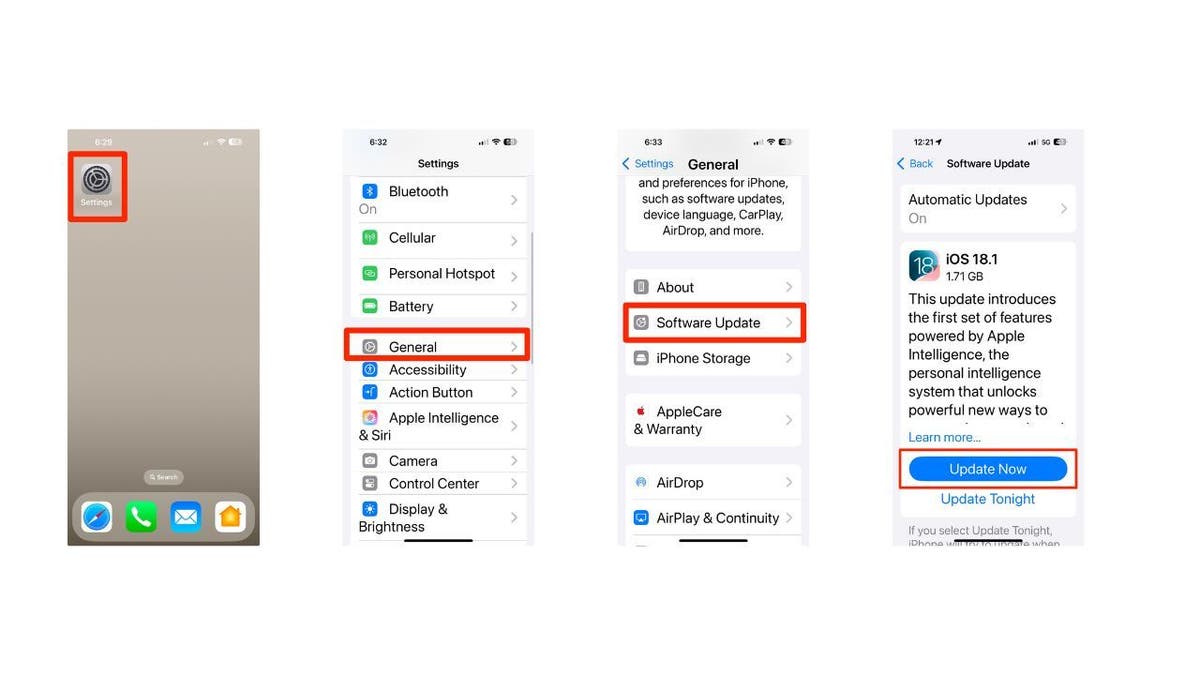
Enabling the Auto-Restart Feature
Ensure your iPhone runs iOS 18.1. Check and update via Settings > General > Software Update > Update Now.
Additional Security Measures
- Strong Passwords: Use unique, strong passwords for each account and consider a password manager.
- Antivirus Software: Install reliable antivirus software on all your devices.
- Regular Backups: Back up your iPhone data regularly through iCloud.
- Two-Factor Authentication (2FA): Enable 2FA for added account security.
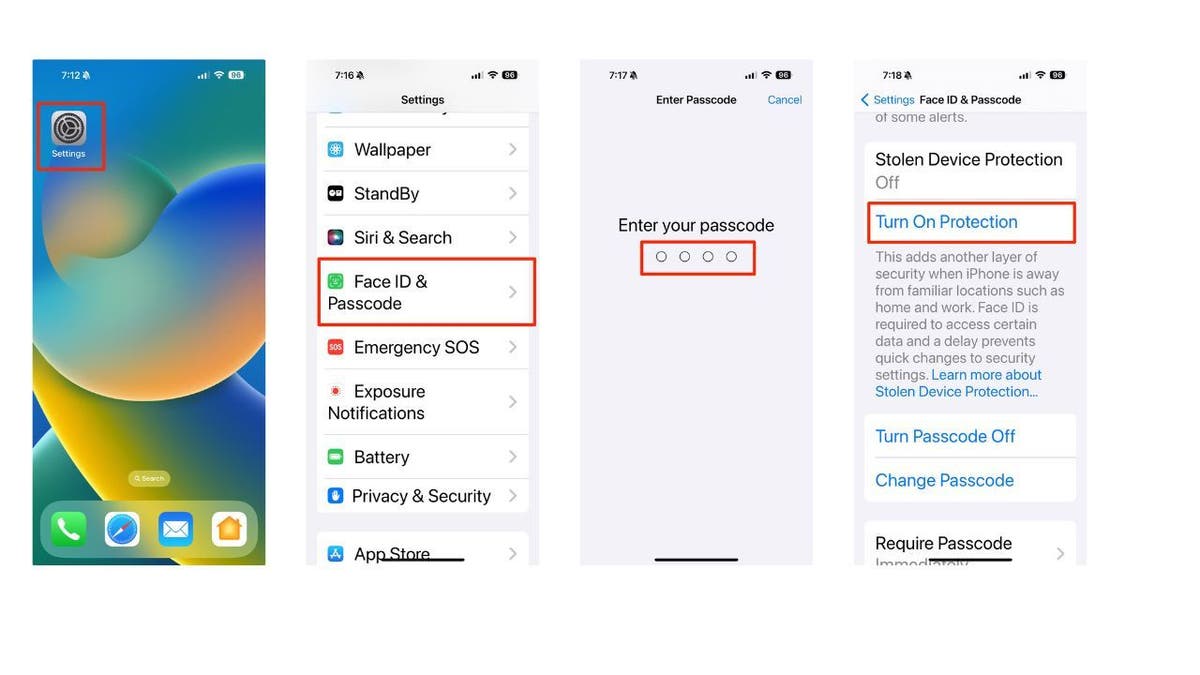
- Stolen Device Protection: Activate this feature to enhance security if your device is stolen.
Key Takeaways
The auto-restart feature significantly strengthens iPhone security. It's a promising advancement in protecting against cyber threats.
Comments(0)
Top Comments